![]() Purpose: list only the ports we need to bring up ONAP on Kubernetes and not expose the cluster to vulnerabilities
Purpose: list only the ports we need to bring up ONAP on Kubernetes and not expose the cluster to vulnerabilities
First defence is a curated incoming/outgoing network security group - see example in OOM-710
There is an issue with certain ports providing API access in Kubernetes up to 1.9 (regardless of authentication lockdown) - we need to work around it until we upgrade to 1.10
https://ip:10250/pods - lists everything
Start with the following back door into kubernetes.
We need to not use a 0.0.0.0/0 cidr for incoming/outgoing network security groups.
use the curated list under
https://wiki.onap.org/display/DW/ONAP+Deployment+Specification+for+Finance+and+Operations#ONAPDeploymentSpecificationforFinanceandOperations-ONAPPortProfile
Still this leaves 8880 vulnerable
https://medium.com/handy-tech/analysis-of-a-kubernetes-hack-backdooring-through-kubelet-823be5c3d67c
ssh:22 access is not the issue -it is protected by a certificate
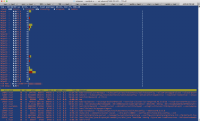
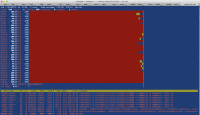
Shutting down the processes is a temporary fix - see screencap
fix
https://github.com/kubernetes/kubernetes/pull/59666
PID USER PR NI VIRT RES SHR S %CPU %MEM TIME+ COMMAND 52144 root 20 0 2071408 53904 1868 S 345.1 0.0 3259:21 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 116483 root 20 0 2137088 54012 1948 S 295.6 0.0 3322:29 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 89198 root 20 0 2137088 54020 1972 S 235.4 0.0 3740:56 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 98302 root 20 0 2071392 54492 1608 S 215.0 0.0 3726:18 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 14793 root 20 0 2136944 54212 1860 S 210.6 0.0 3364:40 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 43524 root 20 0 2137076 55952 1836 S 202.7 0.0 2841:34 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 118090 1001 20 0 2137088 54216 1956 S 185.8 0.0 3087:17 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 70955 ubuntu 20 0 2071528 53908 1692 S 184.1 0.0 3322:54 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 65445 root 20 0 2136944 54256 1888 S 152.2 0.0 3512:16 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 129922 root 20 0 2071540 53836 1792 S 136.3 0.0 3028:14 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 23308 ubuntu 20 0 2071552 54100 1968 S 135.4 0.0 3013:55 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 107922 ubuntu 20 0 2071528 54124 1736 S 122.1 0.0 3517:29 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 126803 ubuntu 20 0 2071528 54308 1688 S 104.4 0.0 3463:55 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 107640 root 20 0 2137080 53920 1904 S 102.7 0.0 3743:06 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 79645 ubuntu 20 0 2137064 54032 1980 S 97.3 0.0 3290:51 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 15970 root 20 0 4781880 559560 51692 S 96.5 0.4 1864:06 kubelet --kubeconfig=/etc/kubernetes/ssl/kubeconfig --allow-privileged=true --regis on some servers you kill everything - it will be back ubuntu@cd-r:~$ sudo ps -ef | grep stratum root 51234 6720 99 04:36 ? 00:05:45 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B another machine 16782 root 20 0 468332 9548 1168 S 59.6 0.1 3364:20 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 15924 ubuntu 20 0 392688 7824 1444 S 51.0 0.0 9151:18 /tmp/udevs -o stratum+tcp://pool.supportxmr.com:3333 -u 45RxEpN2gmd4tnDx3c6EEb7o6Lb46FSvmgiS68ELp1pnCU81+ 17514 root 20 0 468332 9668 1288 S 46.7 0.1 1984:54 /tmp/udevs -o stratum+tcp://pool.zer0day.ru:8080 -u NewWorld -p NewWorld --safe -B 16229 root 20 0 392552 5396 1360 S 27.8 0.0 7755:07 /tmp/udevs -o stratum+tcp://pool.supportxmr.com:3333 -u 45RxEpN2gmd4tnDx3c6EEb7o6Lb46FSvmgiS68ELp1pnCU81+ 11735 root 20 0 2073452 155044 54128 S 4.6 1.0 3063:36 kubelet --kubeconfig=/etc/kubernetes/ssl/kubeconfig --api_servers=https://kubernetes.kubernetes.rancher.+
- blocks
-
LOG-320 CD: OOM deployment templates for public cloud (Arm, CloudFormation, Heat)
-
- Closed
-
-
LOG-410 crypto honeypot 16g VM for intrusion research
-
- Closed
-
- relates to
-
LOG-321 CD: Oneclick Microsoft Azure ARM template for Kubernetes VM install and OOM deployment
-
- Closed
-
-
SECCOM-36 •Security of CI/CD of ONAP– signature verification of artifacts + artifacts
-
- Open
-
-
LOG-895 Upgrade Rancher to 1.6.25 to address CVE-2018-1002105 and move to Kubernetes 1.11.5 (server side)
-
- Closed
-
-
OOM-868 Azure - CPU saturation after running two days without load - Amsterdam
-
- Closed
-
- links to
- mentioned in
-
Page Loading...